Information Security
BigChange treats data protection as a core operational commitment, not an afterthought. Our information security management systems, controls, and policies are continuously reviewed and improved — giving CIOs, CTOs, and business leaders the assurance that your data is handled with the care your business demands.
Our Commitment
Security isn't a feature. It's a foundation.
At BigChange, protecting the data our customers trust us with is a fundamental business obligation — not a compliance checkbox. Our information security management system gives us the framework to identify risks, set clear objectives, and continuously raise the bar on how we protect information across our operations and supply chain.
We hold ourselves accountable to the same standards we'd expect from any partner handling data this critical. That means every control, every process, and every supplier relationship is held to a consistent standard — so our customers, partners, and stakeholders can be confident their data is in safe hands.
.png)
Fred Voccala
Chairman and CEO
Our People
All staff are externally vetted before having access to systems, and more importantly, your data. Our checks include:
.svg)
Right to work
.svg)
Address history
.svg)
Employment history
.svg)
Character reference
.svg)
Basic criminal record check
.svg)
Personal credit check
Our Processes
Your operations depend on ours. We take that seriously.
Our objective is to transform your internal processes; therefore we believe in leading the way with our own.

Our Cloud Provider
The infrastructure behind BigChange is built to the highest security standards in the industry.
BigChange is hosted on Amazon Web Services, a platform trusted by financial institutions, public sector bodies, and global enterprises where security and compliance are non-negotiable. Our customers inherit the benefit of AWS's physical datacentre controls, extensive cloud security services, and a compliance programme that covers some of the most rigorous regulatory frameworks in the world.
Our Architecture
As BigChange leads the way in Mobile Workforce Management, it was essential that we partner with the leader in cloud platforms.
High level
Our cloud architecture provides a multi-region (geography), multi-datacentre solution, that leverages automation and "designing for failure" from inception.
Data and processing are replicated across multiple availability zones synchronously and asynchronously to provide the perfect balance of performance and resilience.
By default production is operated Active/Active over multiple availability zones in a single region/country, with secure data archived to a second region.
Multiple datacentres
Synchronous data replication
Auto-scaling of processing (designed to mitigate component failures)
Multiple regions (countries) for secure data archive

Security controls
Our security controls include but are not limited to:
Encryption
Client connectivity: restricted to minimum TLS v1.2
Data-at-Rest: all object and block storage is encrypted
Data-in-Transit: all external and internal connectivity within the environment is encrypted via minimum TLS v1.2
Networks
Perimeter Network: all servers reside on private networks, with any Internet ingress being traversed via Layer 4 or 7 Application Load Balancers.
Internal Network: all servers are assigned to a security group (controlled outside the host), therefore moving network security to a host level rather than at a subnet level. (e.g. Only the load balancers can connect to the web servers on a specific port etc.)
Authentication
Multi-Factor Authentication Option: set up by default for all new customers (& mandatory for BigChange internal users)
IP Restriction: BigChange customers' administrators manage user access profiles restricting functionality & data groups, setting authorization limits and (if required) limiting IP
Further controls
Segregation: each customer's data is logically partitioned
Continuity: a comprehensive data backup regime is in place which includes full, incremental and continuous backups stored within the AWS environment and stored across multiple regions
Regular Penetration tests: conducted by independently accredited 3rd party testers
Continuous Vulnerability Scanning: using class-leading software to detect and inform of vulnerabilities
24/7 SOC across the full environment: with leading intrusion system to catch anomalous traffic
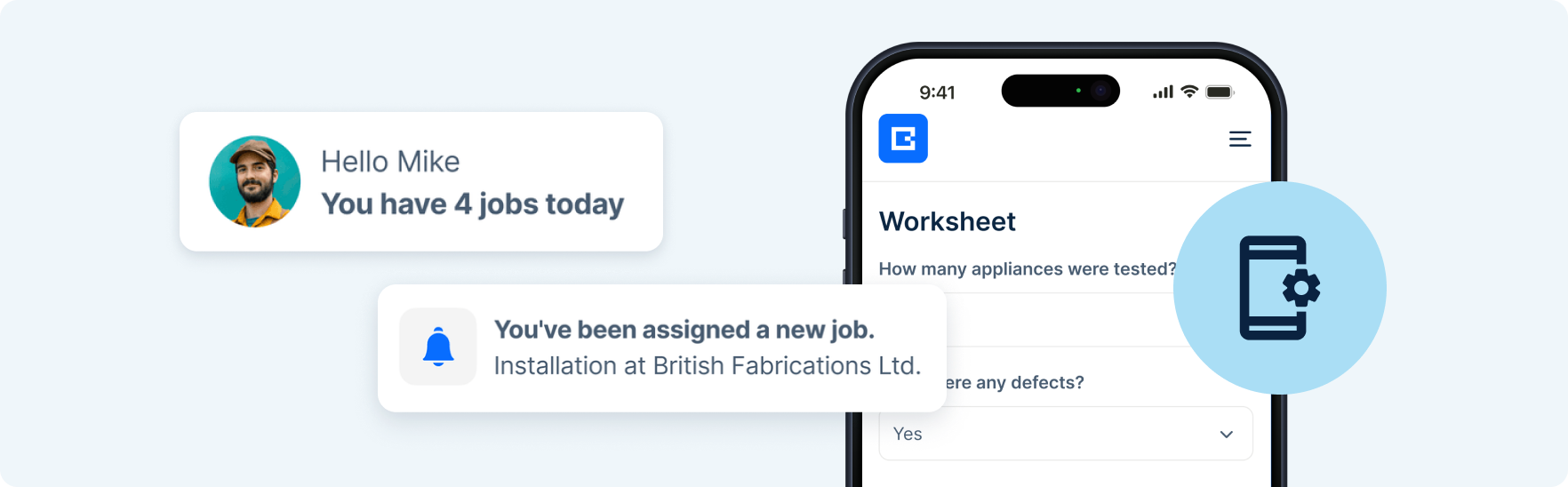
Our App Security
Built securely. Kept secure.
Security is embedded into how BigChange apps are built, not applied after the fact. Developers are screened before accessing our DevOps systems, and all development follows a formal Secure Development Policy — with data confidentiality, integrity, and availability risks assessed and tested in every release.
In the field, all app-to-system communications are encrypted, and BigChange tablets are managed through mobile device management software — enforcing security settings, blocking unauthorised installs, and enabling remote wipe if a device is ever lost or compromised. Regular independent penetration testing keeps our security posture current, with findings acted on across scheduled maintenance releases.
Our Privacy
Privacy isn't a policy document. It's how we operate.
BigChange maintains a structured approach to UK and EU data protection compliance — with clearly defined responsibilities, regular staff training, and a designated Data Protection Officer accountable for oversight across the organisation.
Personal data is inventoried, mapped, and processed only on a documented legal basis. Privacy by design is embedded in how we build and run our systems, backed by regular impact assessments, data subject request processes, and ongoing audits that keep our practices current and compliant.





